Secure Your World, Seamlessly.
Select a solution category below to explore enterprise-grade deployments.
MFA²
Next-gen passwordless and multi-factor authentication spanning the entire tech stack.
Shield
Real-time threat protection, deep packet inspection, and web filtering mapped to your fleet.
Guard
Deep endpoint telemetry, posture assessment, and compliance enforcement across your enterprise.
There are defining moments when a single product fundamentally rewrites the rules. It strips away years of complexity, shifts our entire perspective, and changes how we look at the boundaries of what is possible.
That is 1Key.
Identity & Access.
Where are you authenticating identity?
Server / Workstation
Secure local desktop rendering and offline-capable authentication.
Enterprise SSO (SAML & OIDC)
Frictionless single sign-on access scaling seamlessly across your connected cloud and SaaS applications.
ZTNA Tunnels
Identity-bound, clientless zero trust network access bridging securely into your infra.
RADIUS / LDAP Gateways
Modernize your existing VPNs and legacy firewalls with step-up biometric MFA without altering core configs.
Unified OS Architecture.
A single ecosystem governing the entire local hardware lifecycle.
Unlocking the Computer
Before Windows ever loads, Badger Gate intercepts the login screen, demanding an encrypted MFA push from your phone before granting access to the system.
Inside the Desktop Session
Once you are successfully logged in, Badger Guard operates silently in the background continuously monitoring device posture, web traffic, and enforcing enterprise compliance.
Badger Gate Deployments.
Select a demonstration sequence for Workstation Pre-Login.
Push Approval
Frictionless workstation login via targeted push notifications.
Dynamic QR
Scan-to-login for shared workstations, ensuring zero local data trace.
Badger Guardian Deployments.
Select a demonstration sequence for Workstation Post-Login.
Push Approval
Enterprise MFA gateway for sensitive applications inside the OS.
Dynamic QR
Offline and high-security step-up MFA authentication via dynamic QR.
Badger Gate: Push Approval
True Passwordless Workspace Authentication powered by Device Context.
True Passwordless (PIN or No PIN)
Eliminate credential theft. Employees approve logins directly from their mobile devices using native biometric integration (FaceID / TouchID). Require a custom PIN only when security contexts dictate.
Geo-Fencing & Impossible Travel
Built-in Zero Trust intelligence automatically blocks Push Requests originating from unexpected geographical locations or instances where travel velocity is physically impossible.
Computer Telemetry Checks
Authentication is gated by real-time hardware posture checks. If the origin requesting device fails AV compliance or OS patching standards, the Push is never generated.
Badger Gate: Dynamic QR
Secure Shared Kiosk Access with Zero Trace Credentialing.
Air-Gapped Access
Authenticate even when the workstation is completely offline using time-based cryptographic QR sequence negotiation.
Kiosk & Healthcare Ready
Perfect for shared nursing stations or factory floors. Scan the screen securely from a trusted mobile endpoint to instantly inject your profile seamlessly.
Badger Guardian: Push Approval
Granular Step-Up Authentication for High-Risk Actions.
Privileged Context Gating
Trigger a secondary 1Key Push Approval before users attempt to escalate privileges, uninstall critical software, or execute restricted remote commands.
Session Lockdown
Any failure or denial of a Guardian Push immediately locks out the active terminal, terminating malicious lateral movement.
Badger Guardian: Dynamic QR
Offline Administrative Escalation Made Simple.
Air-Gapped Admin Access
Administrators can securely elevate privileges on disjointed or air-gapped domain controllers specifically by validating a cryptographic QR on their mobile device.
1Key Identity: Enterprise SSO
Extend your native desktop authentication directly into your cloud architecture.
SAML 2.0 & OIDC Identity Provider
Seamlessly integrate your existing enterprise SaaS applications like Salesforce, M365, and Slack behind a singular, impenetrable authentication identity.
SCIM 2.0 Directory Sync
Automatically provision and deprovision users from Azure AD, Google Workspace, and JumpCloud without lifting a finger.
Passwordless Passkey Synchronization
Allow your users to authenticate using WebAuthn/FIDO2 credentials (like Face ID or Windows Hello) that sync securely across their devices.
Remote Access: ZTNA Tunnels
Identity-bound, clientless zero trust network access bridging securely into your infra.
Deep TCP Reverse Tunneling
Broker secure, end-to-end encrypted connections to your internal infrastructure without exposing legacy VPN ports to the public internet.
Posture Compliance Gates
Automatically deny network tunnel generation if the requesting machine has disabled its local Antivirus or Firewall, guaranteeing a clean network perimeter.
Live Unified Dashboard
Visualize real-time throughput, individual TCP socket states, and orphaned tunnels instantaneously from the centralized administration console.
Legacy Gateways: RADIUS/LDAP
Modernize your older infrastructure instantly via protocol interception.
Zero Configuration Friction
Point your existing Cisco, Palo Alto, or Fortinet VPNs at the 1Key RADIUS proxy to instantly enforce step-up biometric MFA without altering your core firewall configurations.
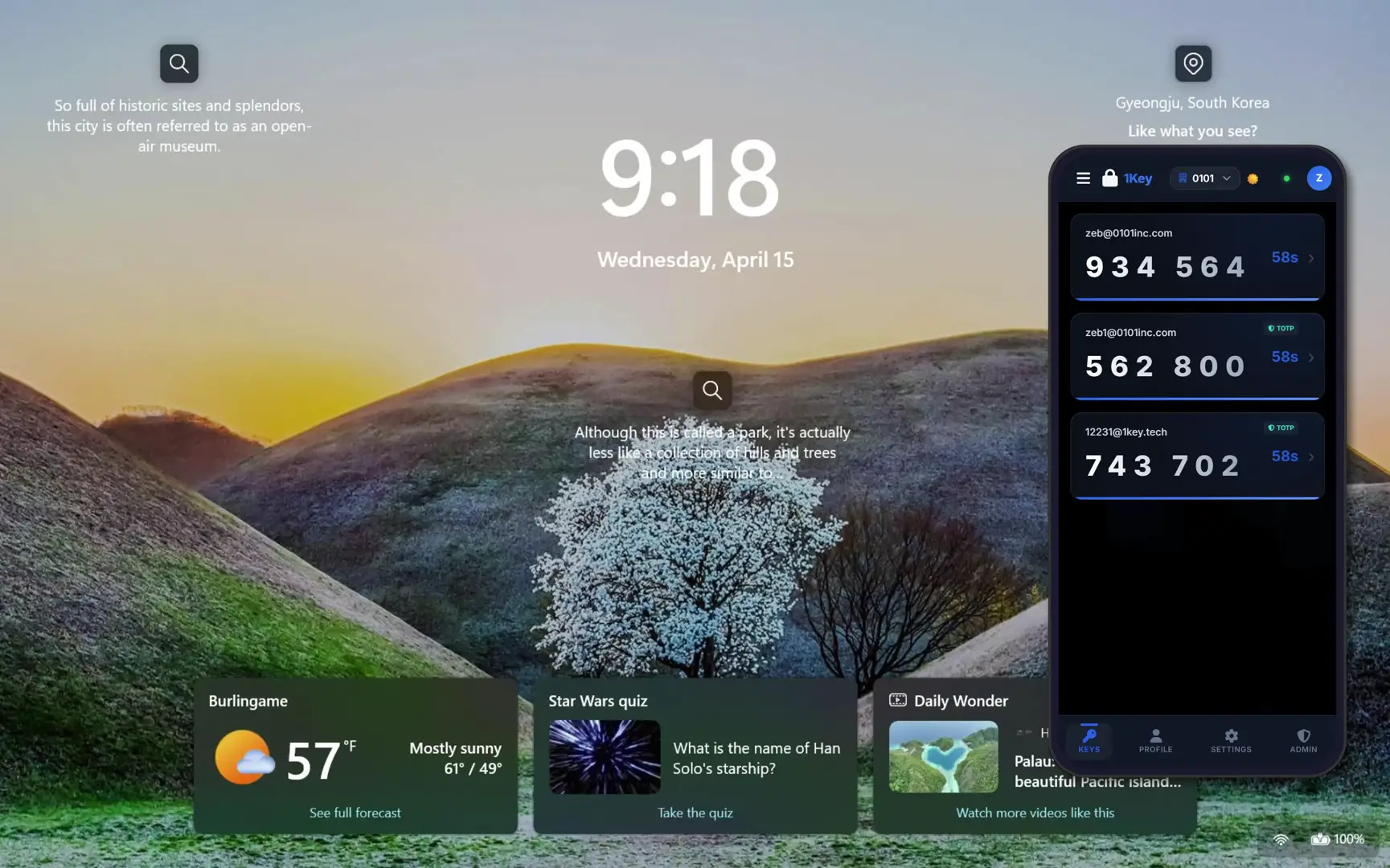
Legacy TOTP Compatability
Automatically ingest and process legacy Google Authenticator or Authy TOTP codes, ensuring a frictionless migration path for your existing userbase.
Badger Shield: Web Security
DNS and HTTPS Deep Packet Inspection deployed directly at the endpoint.
Dual-Stack DNS & WFP Control
Intercept and filter network traffic dynamically using native Windows Filtering Platform hooks alongside localized DNS proxies, preventing bypassing via DoH or IPv6 manipulation.
HTTPS Cert Interception
Automatically generate localized Root CAs to intercept, decrypt, and serve fully white-labeled, branded block-pages even on TLS-encrypted traffic.
Corporate Rule Presets
Quickly deploy sprawling web filtering restrictions leveraging over 150+ dynamically categorized threat lists, or allow users to self-service "Request Access" via the block page.
Badger Guard: Endpoint Control
Deep localized telemetry and mandatory posture compliance analysis.
Expansive WMI/COM Telemetry
Collect and monitor over 30 deeply embedded security and hardware attributes in real-time, tracking everything from BitLocker health to active visual monitor connections.
Vulnerability Auto-Restrictions
Automatically sever application tunneling and limit network access instantly if the local endpoint triggers a zero-day vulnerability alert or degrades its firewall posture.
Stolen Device Kill-Switch
Remotely inject a Session 0 lock command instantly from the admin console, or violently terminate all inbound network pipelines by flagging the hardware as stolen.